Zero Trust is not a single architecture nor solely a property of a cybersecurity-based product. Identifying the gaps in the traditional Trusted Internet Connection (TIC) model can help describe the origin of the problem, Zero Trust is intended to resolve. This is also described in NIST SP 800-207.
“A typical enterprise’s infrastructure has grown increasingly complex. A single enterprise may operate several internal networks, remote offices with their own local infrastructure, remote and/or mobile individuals, and cloud services. This complexity has outstripped legacy methods of perimeter-based network security as there is no single, easily identified perimeter for the enterprise. Perimeter-based network security has also been shown to be insufficient since once attackers breach the perimeter, further lateral movement is unhindered.”
Zero Trust is a strategic approach to cybersecurity whereby data and service protection are the focus assuming that given a perimeter breach, any enterprise asset or environment is no more trustworthy than another. This lack of implicit trust inherently protects against lateral movement by continuously analyzing and evaluating risks to data, assets, and applications, while also enacting protections.
Zero Trust Principles
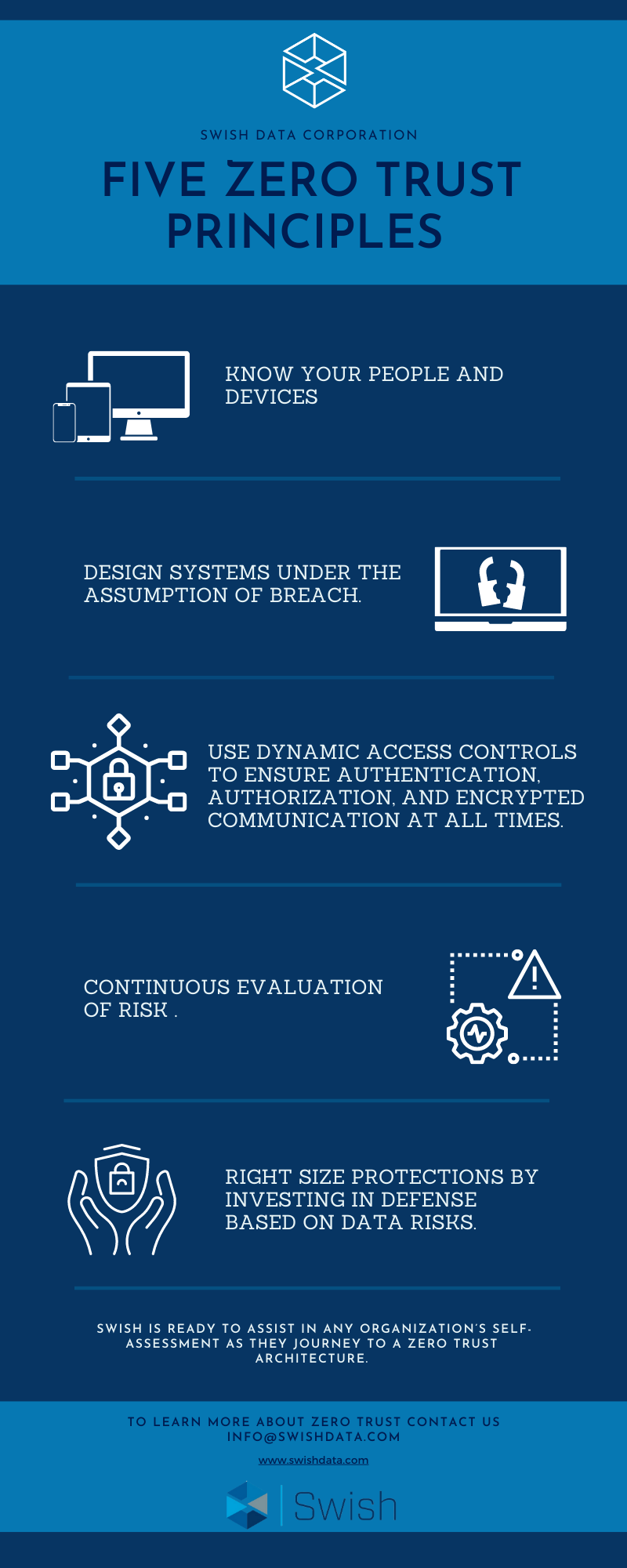
- Know your people and devices.
- Design systems under the assumption of breach.
- Use Dynamic Access Controls to ensure authentication, authorization, and encrypted communication at all times.
- Continuously evaluate risk.
- Right-size protections by investing in defense based on data risks.
As a set of guiding principles for workflow, system design, and operations, transitioning to a Zero Trust architecture can improve the security posture of any environment. With that in mind, the shift is more of an organizational journey as opposed to a 1:1 replacement of hardware/software.
The good news is that many agencies already have elements of a Zero Trust architecture in their enterprise and incrementally implementing Zero Trust principles, process changes and technological solutions over time can ultimately lead an agency to the desired outcome.
Swish is continuously engaged with federal customers in guiding their cybersecurity implementations while maintaining close relations with top vendors in the space to ensure customer success. The Swish team, under the cybersecurity pillar of our Center of Excellence, is ready to assist in any organization’s self-assessment as they journey to a Zero Trust architecture and the realization of a demonstrably more secure enterprise.
To learn more, contact us!





