Digital Twin for IT & Cyber
Unlocking IT Excellence with Faster MTTR, Increased Security, and Better Stability!
How many problems can you solve with a Digital Twin for IT and Cyber?
The Challenge
Consider this all-too-familiar challenge: You are on an emergency bridge call for a major availability or security incident, and the very first question that is usually asked is: “What has changed?”
Incidents can cost government agencies millions of dollars and cause severe damage to reputation and mission outcomes. Conventional monitoring tools are usually not much help. They collect metrics and raise alerts, but provide few answers to what has actually changed. So, you spend valuable time asking questions and sorting through change tickets piecing together the possible change scenarios.
In contrast, envision a Digital Twin for IT and Cyber solution that tracks extensive configuration and security settings across your entire enterprise, including applications, infrastructure, and cloud and on-premises environments; and could automatically identify risky unauthorized changes and security vulnerabilities. This Digital Twin for IT and Cyber solution could be integrated into your root cause analysis engines to trigger auto remediation procedures before most users or services even notice a glitch.
So, how many problems could you solve with a Digital Twin for IT and Cyber solution?
A New Way is Needed
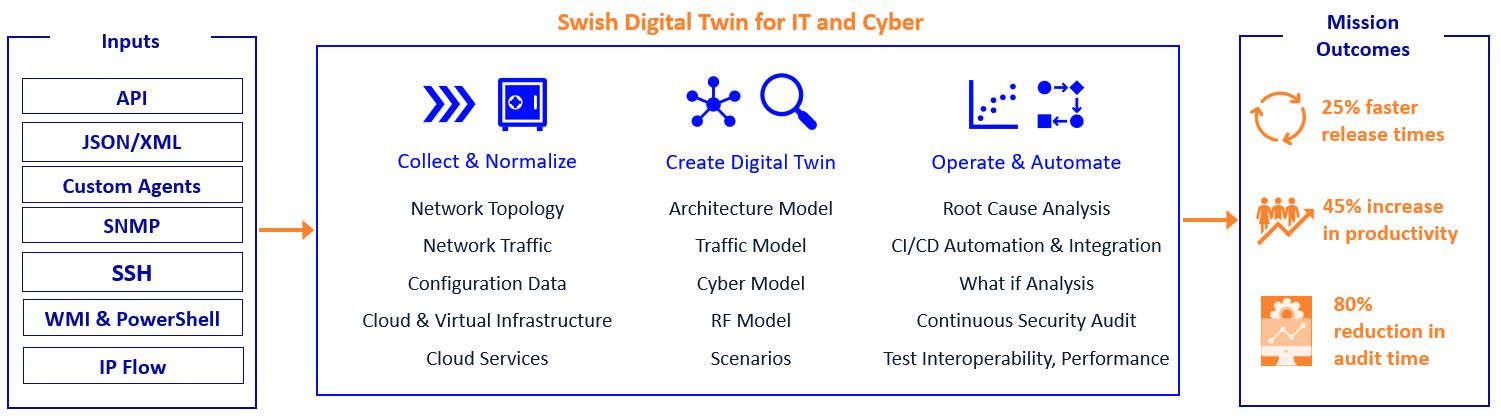
Swish, your trusted partner for public sector IT solutions, has teamed with best-of-breed technology vendors, to bring you a highly integrated and automated approach to change and risk detection with our Digital Twin for IT and Cyber solution. In the ever-evolving lT landscape, the concept of a Digital Twin has emerged as a game-changer. Imagine a virtual replica of your entire IT ecosystem – from applications to network infrastructure to security – providing real-time insights, predictive analytics, and actionable answers. Welcome to the future of IT operations.
Welcome to the future of IT operations.
- Applications are the heart of every IT infrastructure – the software that powers productivity, innovation, and engagement with citizens and employees. With the Digital Twin IT and Cyber solution, you gain unprecedented visibility into the performance, health, and dependencies of your applications. Accelerate troubleshooting, audit changes, manage consistency, detect drift, score changes based on risk impact, predict potential issues and more.
- DevOps and SRE practices are essential in today’s fast-paced development environment, to accelerate innovation and enhance collaboration between development and operations teams. Swish’s Digital Twin IT and Cyber solution enables simulation and testing, leverages predictive analytics, facilitates collaboration and communication, automates optimization, and mitigates risks throughout the software development and deployment lifecycle.
- Network form the backbone of modern IT infrastructure, facilitating seamless communication, data transfer, and collaboration. With a Digital Twin IT and Cyber solution, you can visualize your network topology in intricate detail, from routers and switches to subnets and traffic flows. Understand path characteristics, discover end-to-end MTU limitations, validate golden configurations, understand the blast radius for an incident, predict network congestion, and simulate network changes before implementation; minimizing downtime and maximizing efficiency.
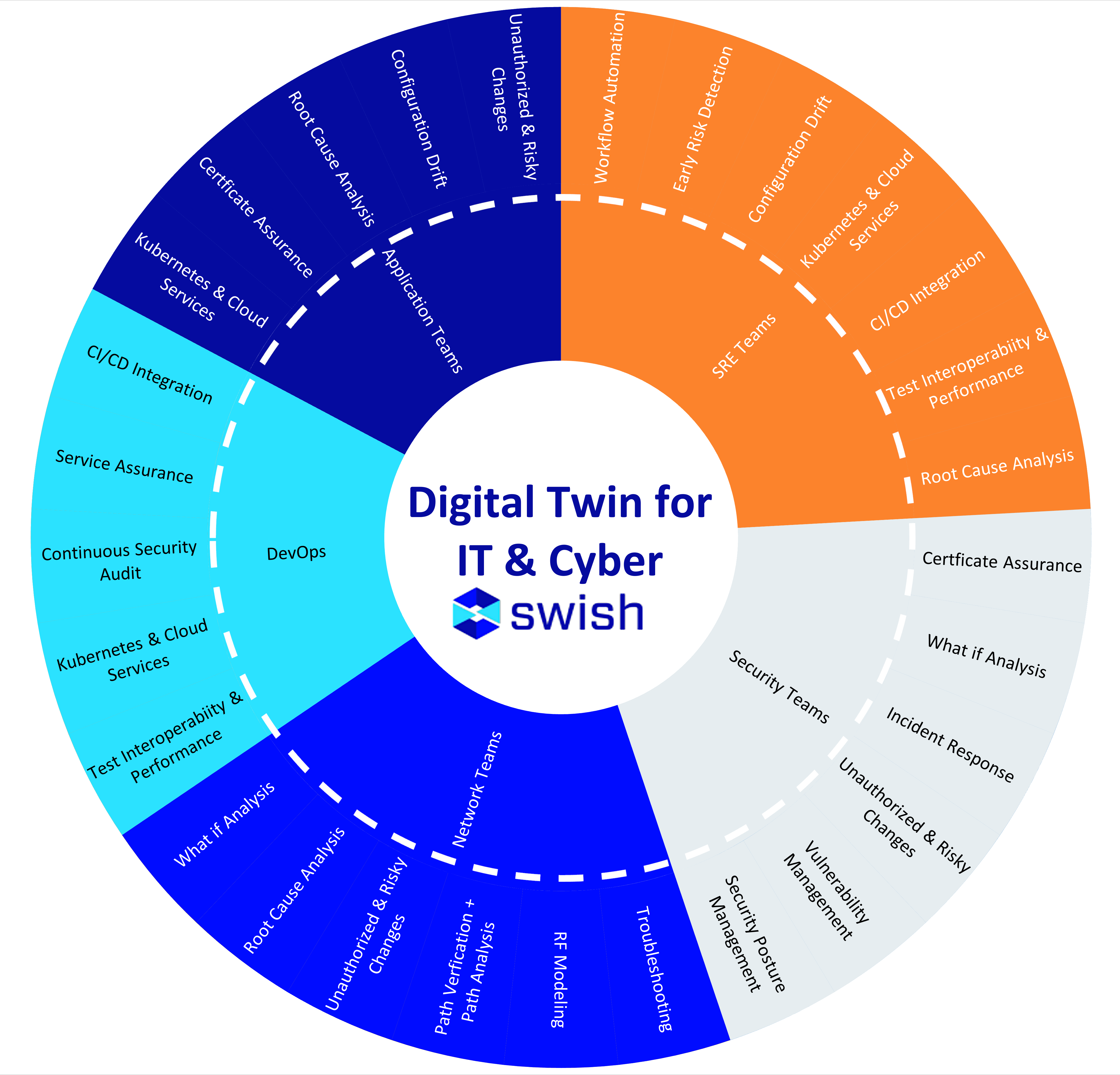
- Security is critical in an era of escalating cyber threats and regulatory compliance. A Digital Twin empowers organizations to fortify their defenses and mitigate risks with unparalleled precision. Model your security posture comprehensively, from access controls and encryption protocols to zero trust and compliance audits. Detect and respond to security incidents swiftly, leveraging AI-driven anomaly detection and behavior analytics to thwart emerging threats before they escalate. Conduct virtual security audits, assess compliance with industry standards, easily find all unauthorized changes, and simulate cyberattack scenarios to reinforce resilience and readiness.
Key Takeaway
A Digital Twin for IT & Cyber represents a paradigm shift in how organizations plan, analyze, and troubleshoot. They transcend traditional silos and empower holistic, data-driven decision-making. By harnessing the power of digital twins across applications, network, and security domains, organizations can unlock new levels of agility, insights, and innovation in the digital age. Welcome to the future of IT operations with Swish’s Digital Twin for IT and Cyber.
Benefits
According to customer studies, when using Swish’s Digital Twin for IT and Cyber solution, IT teams experience:
- Enhanced Agility: Adapt rapidly to changing business requirements and technological trends with actionable insights and predictive analytics.
- Improved Uptime: Fine-tune your applications, network, and security configurations for peak efficiency and reliability, minimizing downtime and maximizing productivity.
- Heightened Security: Bolster your cyber defenses and safeguard sensitive data with proactive threat detection, rapid incident response, and continuous compliance monitoring.
- Cost Savings: Streamline operations, optimize resource utilization, and mitigate risks effectively, driving down operational expenses and maximizing ROI.
Did you know Gartner estimates that 85% of incidents are contributed to changes in your Enterprise?
![]()
The Solution
Swish Digital Twin for IT and Cyber solution takes advantage of COTS technology from trusted Swish OEM partners leverages Swish services to plan, implement, manage and drive optimization. This includes the platform management cluster, data collection via agents and telemetry, 3rd party integrations and adoption services in the environment of your choice including AWS, Azure, or on-premises environments. The deployment complies with the stringent security and compliance requirements, including National Institute of Standards and Technology (NIST) Risk Management Frameworks and Department Information Systems Agency (DISA) Security Technical Implementation Guides (STIGs).
Swish Advantage
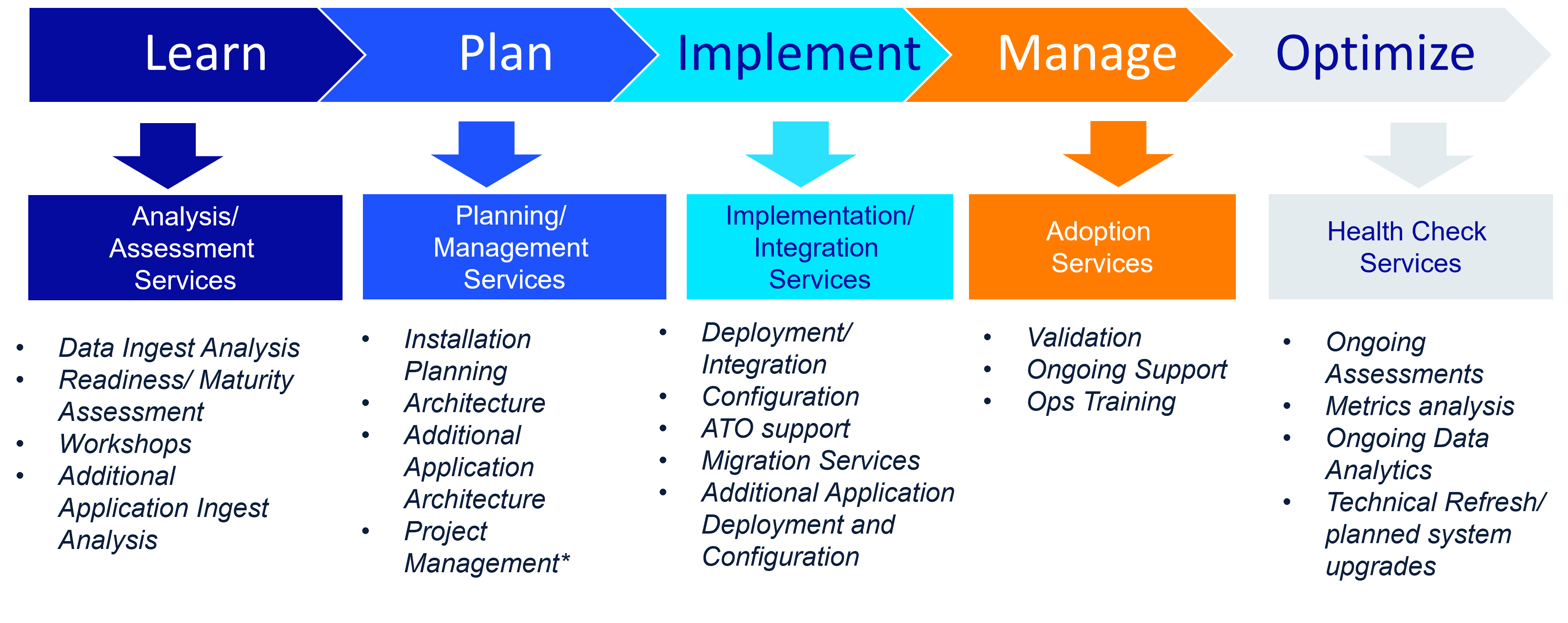
The Digital Twin for IT and Cyber requires not only the enabling technologies, but the intellectual property required to adopt, integrate, and realize mission value. The Swish Services team, with years of experience and a proven framework for delivering mission value for government clients, works with your organization to ensure the success of the Digital Twin for IT and Cyber solution. Swish provides a vast array of services including strategic planning workshops, performance maturity workshops, basic implementation services, staff augmentation, and fully managed services offerings. These offerings are designed to drive hyper-scale adoption across your enterprise when paired with our proven customer success journey.
We have a deep understanding of the acquisition management process and bidding compliant, best-value proposals. Swish solutions are available from our various contract vehicles.
Get Started
Request a meeting with our experts or email Swish at info@swishdata.com to request more information.
Compliance & Certifications
Swish Data and our technology partners prioritize customer security and reliability concerns by leveraging a four-pillar approach to delivering secure and dependable solutions. All of our solutions comply with National Institute of Standards and Technology (NIST) [NIST SP800-37 and SP800-53] and Department Information Systems Agency (DISA) Security Technical Implementation Guides (STIGs).
- Security – Swish is continuously refining its security strategy and framework to reflect our organizations specific security risks. Maintaining a robust security-first culture is key to protecting the integrity of our products and services, inspiring customer confidence, and furthering our business relationships.
- Privacy – Swish knows that customers care about how personal data is used and shared, and Swish takes privacy very seriously. Swish’s privacy and risk management framework is designed to meet Swish’s obligations under applicable federal and state privacy laws.
- Compliance – Swish undergoes third-party audits and obtains certifications to provide our customers with independent, third-party Assurance.
- Reliability – Swish and our technology partners design our offerings to deliver secure, highly available solutions, 24-7, around the globe to support our federal customers regardless of where they are.