AI Powered Configuration Risk Intelligence
Faster MTTR, Fewer Incidents, Better Stability!
The Challenge
Consider this all-too-familiar challenge: You are on an emergency bridge call for a major application outage, and the very first question that is usually asked is: “What has changed?”
IT outages and emergency bridge calls are a nightmare to everyone involved. Outages cost agencies billions of dollars and cause severe damage to the overall agency mission outcomes. Conventual monitoring tools usually not much help in this scenario, they collect metrics and raise alerts, but provide little answers to what has changed. So, you spend valuable time asking questions and sorting through change tickets piecing together all the various change scenarios.
In contrast, envision an automatic AI Powered Configuration Risk intelligence platform that tracked extensive configurations across your entire enterprise, including applications, infrastructure, in both cloud and on-premises environments that could automatically identify risky and unauthorized changes to your environment and trigger auto remediation procedures before most users even notice a glitch.
A New Way Is Needed
Swish and the Market-leader in change detection, Evolven, have teamed to bring the AI Powered Configuration Risk Intelligence platform to Public Sector customers.
The AI Powered Configuration Risk Intelligence platform offers a unified risk-based view of configurations and changes across the end-to-end hybrid cloud, empowering IT teams to proactively and automatically safeguard their enterprise. The platform utilizes comprehensive and granular configuration data analysis with patented AI-based analytics to quickly detect potential misconfigurations and risky changes, thus reducing the risk of costly security breaches, regulatory non-compliance, and downtime.
The AI Powered Configuration Risk Intelligence platform is built upon two foundational layers: Discovery and Risk Analytics.
- Discovery – Unlike any other discovery technologies in the market, our solution out-of-the-box collects granular configuration across the end-to-end hybrid, multi-cloud environment, while frequently monitoring for changes with extremely low overhead. Configurations include application artifacts, configuration files, database schemas, master data, OS kernel, network routing tables, firewall rules, Kubernetes platform parameters, Docker images, and much more.
- Analytics – the patented AI-based Risk Analytics engine provides valuable insights into the configuration and change data collected by the discovery process, highlighting potential misconfigurations and risky changes. In addition, the Analytics layer includes powerful and flexible Search and Policy engines.

Additional Resources
The platform capabilities are structured around the Configuration Risk Center and the Change Risk Center to mitigate a wide range of configuration and change risks.
Change Risk Center:
- Unauthorized Change Detection – detect and report any changes that were executed without approval.
- Change Audit and Reconciliation – automatically reconcile actual changes with the approved change tickets, CI/CD pipeline deployments, automated infrastructure deployments, and more.
- CI/CD Risk Gateway – estimate risks of configuration and code changes going through the CI/CD pipelines.
- Drift Detection and Consistency Analysis – detect and analyze consistency across comparable servers and across Prod, pre-Prod, and DR environments.
- File Integrity Monitoring (FIM) – detect, report, and prioritize changes made to the target files and their configuration parameters based on associated risk.
- Root Cause Analysis (RCA) – correlate actual changes with alerts and incidents and analyze those changes to identify the root cause.
Configuration Risk Center:
- Configuration Asset Inventory – a single source of truth through automated discovery, analysis, categorization, prioritization, and search capabilities for global hybrid IT assets and their detailed extensive configuration.
- Configuration Baseline Management – automatically captures the certified configuration state of a component, host, or application as a baseline and uses it to verify the configurations in your environment.
- Policy Verification – continuously scan, detect, and report on deviations from user defined out-of-the box configuration policies.
- Certificate Assurance – discover all certificate types, and alert owners prior to expiration.
- Vulnerability Detection – detect, verify, and report on vulnerable technology components and configurations (e.g. Common Vulnerabilities and Exposures – CVE .
- Blindspot Detection – detect and report on assets not covered by the required security and monitoring tools.
Value Proposition
When you’re evaluating intelligent solutions, it’s not just about capabilities. It’s about ROI. According to our own internal customer studies, IT Operations, DevOps, and ITSM Teams leveraging the platform saw:
- 50% up faster mean-time-to-resolution (MTTR)
- 35% decrease in the number of incidents
- 35% release-time-to-market (RTM)
- 45% increase in productivity
The Solution
Swish is an Evolven Federal partner focused on providing observability and software intelligence solutions in the U.S. Public Sector. We have over 20 years implementing solutions for our federal clients and have a proven track record of customer satisfaction and mission success. Swish also has cleared individuals to support your most sensitive projects. Swish is VA CVE-certified as a Service-Disabled Veteran-Owned Small Business (SDVOSB) and SBA-recognized as a HUBZone Business.
The AI Powered Configuration Risk Intelligence solution leverages Swish services to deploy the Evolven platform management cluster, collection agents as well as its supporting components, integrations and adoptions services in the environment of your choice including AWS, Azure, or on-premises environment. The deployment complies with the stringent security and compliance requirements of U.S. Federal agency to include National Institute of Standards and Technology (NIST) [NIST SP800-37 and SP800-53] and Department Information Systems Agency (DISA) Security Technical Implementation Guides (STIGs).
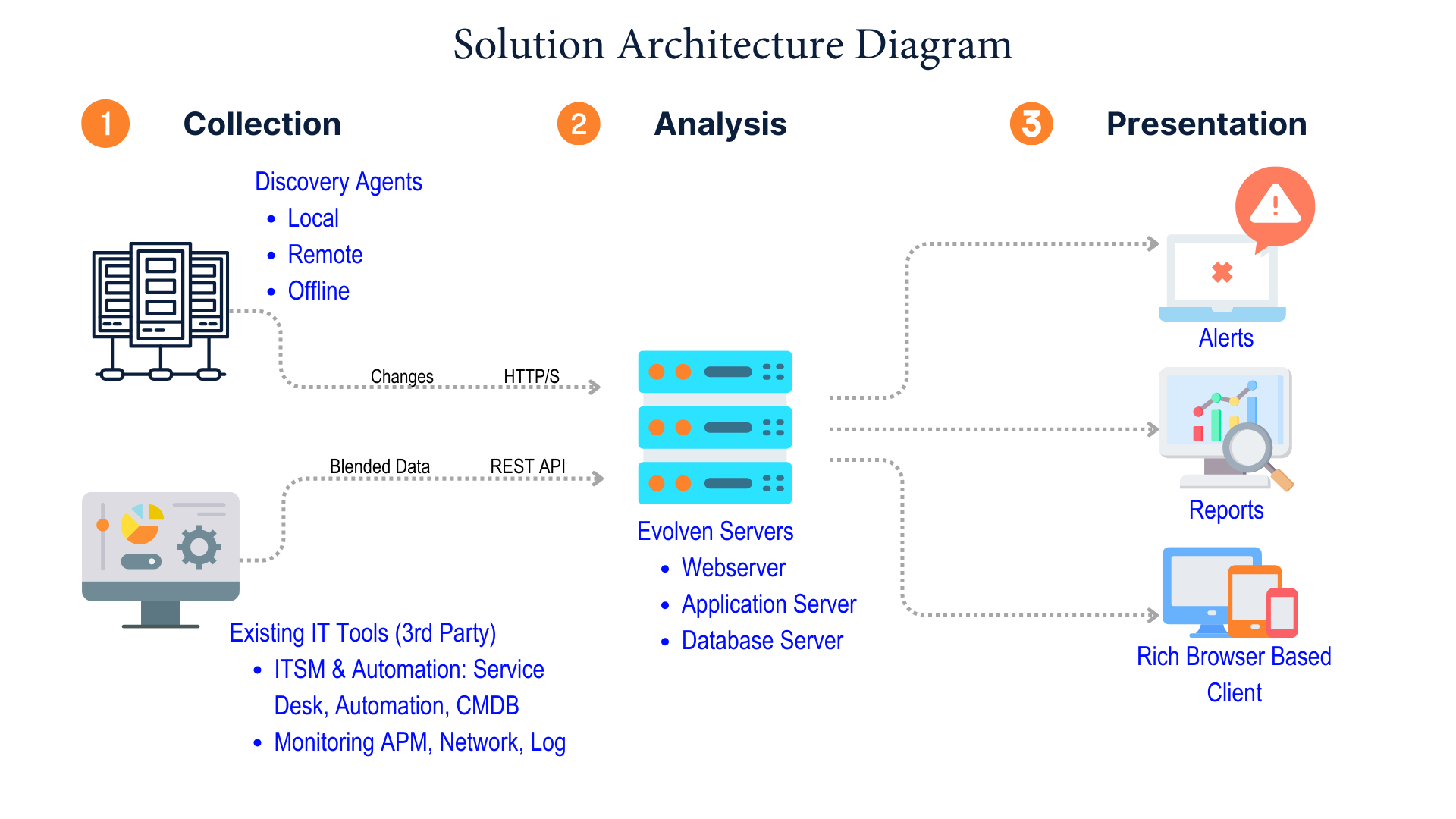
The management cluster consists of three-tiers (Web Server, Application Server, Database Server):
Web & Application Server- Requires Windows 2008 R2 64-bit (or newer) and runs on an embedded Apache Tomcat or WebSphere Application Server.
Database Server – Requires Windows 2008 R2 64-bit (or newer) and MSSQL Server 2008 R2 (or newer)
The agents are push-based (meaning that agents feed information to the application server. The solution agent model is very flexible, and supports various customer requirements:
Local Agents – Run directly on monitored servers and push the delta information to the application server.
Remote Agents – Collect information from remote monitored servers and push the delta information to the application server. These agents run on multi-purpose hosts or hosts dedicated to the agent collection task.
Offline Agents – Run in an ad-hoc manner, either from a mount point or a USB key without actual installation. These agents are run deliberately and collect information locally (into an XML file) that can be uploaded to the application server. They can be used on servers that are blocked by firewalls, or in situations where servers are otherwise disconnected from the application server (for example, an outsourced provider without VPN privileges).
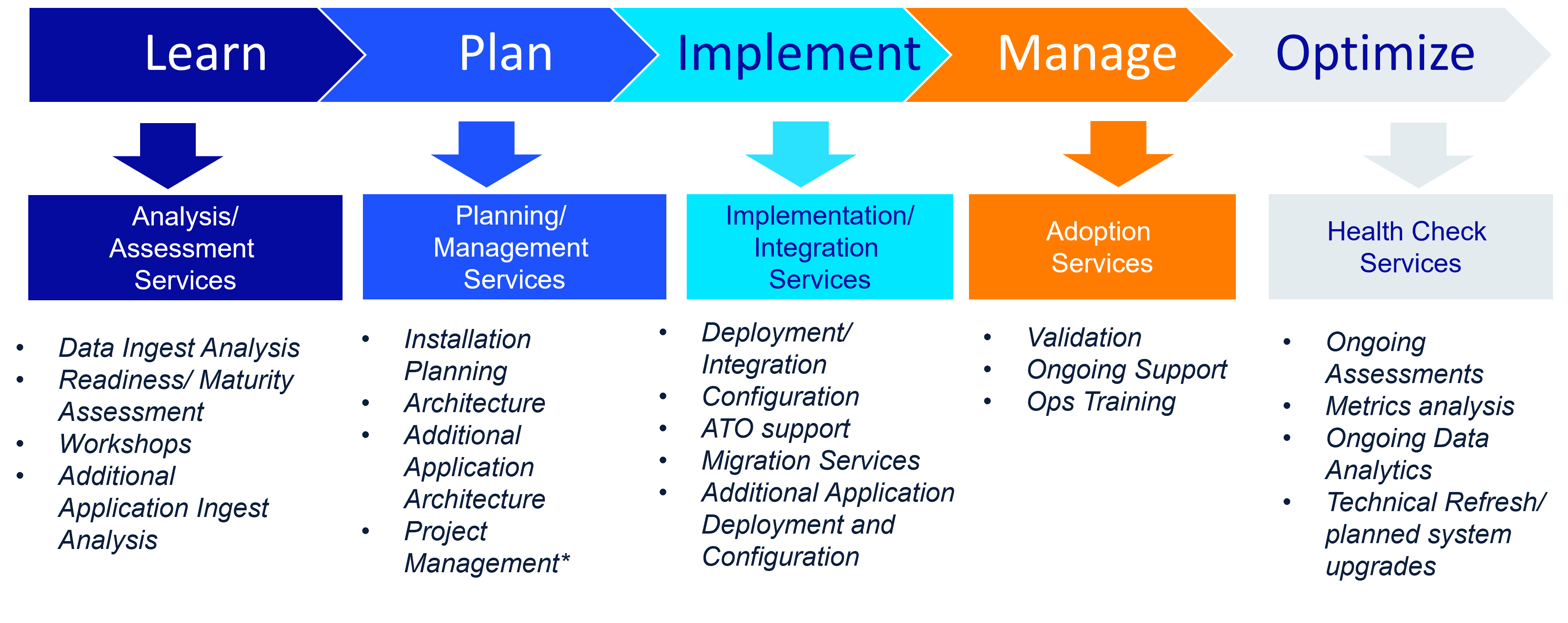
Swish Advantage
The AI Powered Configuration Risk Intelligence solution requires an investment in, not only the enabling technologies, but also in the intellectual property required to adopt, integrate, and realize mission value. The Swish Services team, with years of experience and a proven framework for delivering mission value for government clients, works with your organization to ensure the success of the AI Powered Configuration Risk Intelligence solution. Swish provides a vast array of services including strategic planning workshops, performance maturity workshops, basic implementation services, staff augmentation, and fully managed services offerings. These offerings are designed to drive hyper-scale adoption across your enterprise when paired with our proven customer success journey.
Facilitate Procurement Today
With our AI Powered Configuration Risk Intelligence solution powered by Evolven, your agency can leverage AI based analytics to detect and prioritize risks triggered by changes in configurations across your applications, infrastructure, and data to prevent and resolve stability, compliance and security issues. Additionally, the solution’s adherence to federal IT system controls gives you peace of mind by meeting your security and compliance requirements.
Contact Swish today at info@swishdata.com to learn more about our AI Powered Configuration Risk Intelligence solution and how it can help you unlock the full potential of your applications while achieving the highest levels of security and compliance.
Compliance & Certifications
We take a security-first mindset in all we do, and our commitment extends to ensuring that we maintain the certifications that matter to the Federal Government. The solution is currently ISO27001 certified.