In our first breakdown of the Identity Pillar requirements as outlined in M-22-09, we will discuss the pillar summary, necessary situational awareness items, and action items for agencies responsible for meeting the mandate. This Identity section is broken into three topics: Enterprise-wide Identity Systems, Multi-Factor Authentication, and User Authorization.
Identity – Bottom Line Up Front (BLUF)
- Agencies must employ centralized identity management systems for agency users that can be integrated into applications and common platforms.
- Agencies must use strong MFA throughout their enterprise.
- – MFA must be enforced at the application layer, instead of the network layer.
- – For agency staff, contractors, and partners, phishing-resistant MFA is required.
- – For public users, phishing-resistant MFA must be an option.
- – Password policies must not require use of special characters or regular rotation.
- When authorizing users to access resources, agencies must consider at least one device level signal alongside identity information about the authenticated user.
Enterprise-wide identity systems
Sitatuational Awareness:
Enterprise-wide identity systems require: 1) a holistic view of users with a strong understanding of their responsibilities and authorities and 2) an ability to verify the identities of users when they attempt to access systems.
Users should sign on once and then directly access other applications and platforms also known as Single Sign On. SSO
Action Items:
Do consolidate the means of authenticating to as few agency-managed identity authentication systems as practicable.
Do promote auditable identity practices that should be capable of supporting human authentication through scripts or command-line tools.
Multi Factor Authentication
Sitatuational Awareness:
This memo focuses primarily on the internal enterprise security posture of agencies, but it also strives to equitably balance security and usability with public-facing systems offering users more options for authentication.
Action Items:
Do integrate MFA at the application layer through an enterprise identify service. Where the user will authenticate into applications.
Do use Phishing resistant MFA like (primary) PIV, FIDO2 or W3C’s open “Web authentication” standard.
Do centrally support non-PIV authenticators in the enterprise identity management systems so that they are centrally managed and connected to identities.
Do ensure account recovery process as the exceptional option for users and require high-friction that costly to overcome such as in-person, live video, or other methods.
Do pursue greater use of passwordless MFA as a part of agency modernizes.
Do remove password policies that require special characters and regular password rotation from all systems within 1 year, January 26th 2023.
Do offer phishing resistant authentication on public facing web services that offer MFA within 1 year (by January 26th, 2023).
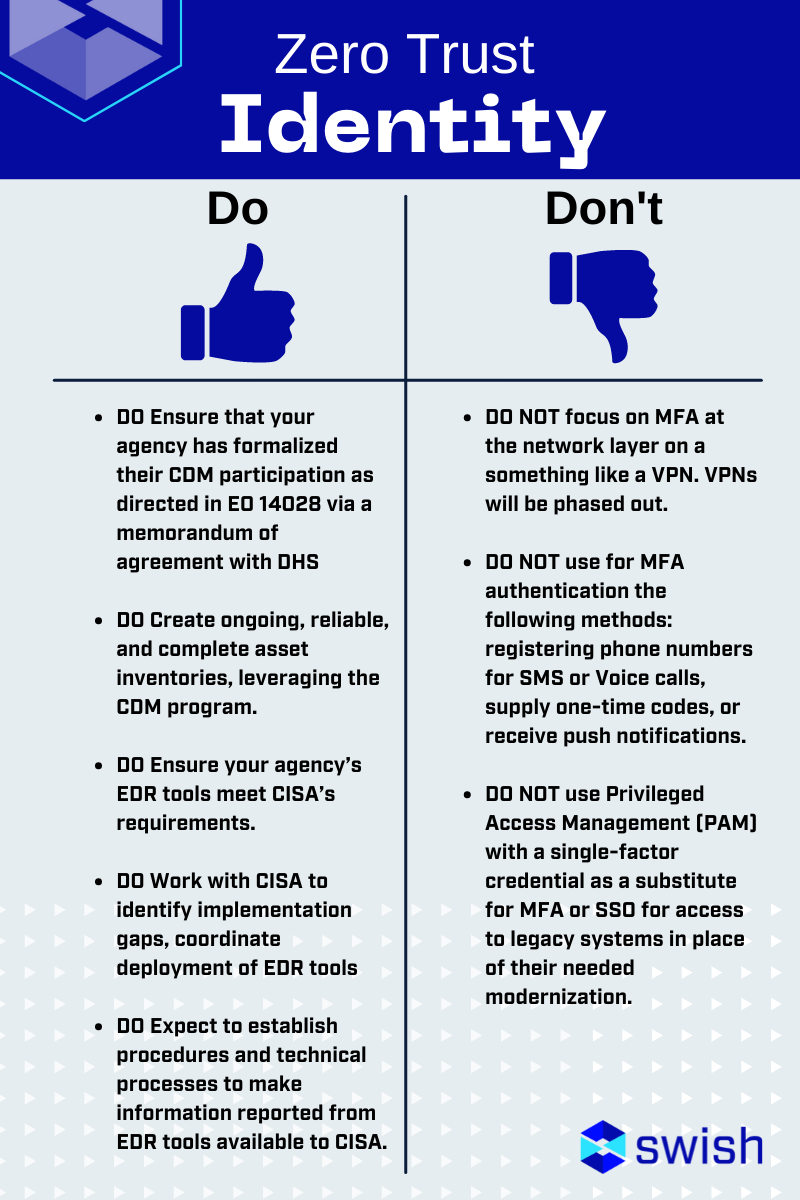
DO NOT focus on MFA at the network layer on a something like a VPN. VPNs will be phased out.
DO NOT use for MFA authentication the following methods: registering phone numbers for SMS or Voice calls, supply one-time codes, or receive push notifications.
DO NOT use Privileged Access Management (PAM) with a single-factor credential as a substitute for MFA or SSO for access to legacy systems in place of their needed modernization.
User Authorization
Sitatuational Awareness:
Currently, Role-Based access control (RBAC) is the focused authorization model for Fed but should incorporate more attribute-based access control (ABAC)
Action Items:
Do evaluate every request for access whether it is appropriate, which requires continuously evaluating any active session.
Do perform authorization on multiple levels using RBAC and ABAC to allow or deny access by enforcing checks based on the user’s identity, attributes of the resource being accessed, and the environment at access time.
Do incorporate at least one device-level signal along with identity information about the authenticated user when regulating access to enterprise resources.
Opportunities for Improvement
Agencies often have multiple identity silos potentially tied to local users in specific applications or databases. This Zero Trust order focuses on the implementation of best practices as well as guidance to centralize the identity checking process to ensure appropriate MFA methods are clearly identified and that user sessions are continually authorized. There are many ways to granularly tighten controls for user access which can be leveraged with additional administrative overhead in combination with compensating controls in other pillars.
This is the second in a series of blog posts on Zero Trust and M-22-09, you can find the first post here. Each week, Swish will publish a new post covering the Summary, Situational Awareness Items, and Agency Action items for each section of the Memorandum. Swish Engineering POCs are available for individual discussions. Contact Us to learn more!





