On January 26th, 2022 the Office of Management and Budget (OMB) released the latest Memo 22-09 tied to the Zero Trust strategy outlined in the Executive Order 14028.
OMB M-22-09 is more prescriptive for agencies with timelines attached and Swish would love to share our thoughts on how this Memo is structured and what your agency can do about it.
Swish will be releasing a Blog Post series that covers the 5 pillars of Identity, Devices, Networks, Applications and Workloads, and Data.
At a high level, the strategy is summarized as:
- Federal staff have enterprise-managed accounts, allowing them to access everything they need to do their job while remaining reliably protected from even targeted, sophisticated phishing attacks.
- The devices that Federal staff use to do their jobs are consistently tracked and monitored, and the security posture of those devices is taken into account when granting access to internal resources.
- Agency systems are isolated from each other, and the network traffic flowing between and within them is reliably encrypted.
- Agency enterprise applications are tested internally and externally and can be made available to staff securely over the internet.
- Federal security teams and data teams work together to develop data categories and security rules to automatically detect and ultimately block unauthorized access to sensitive information.
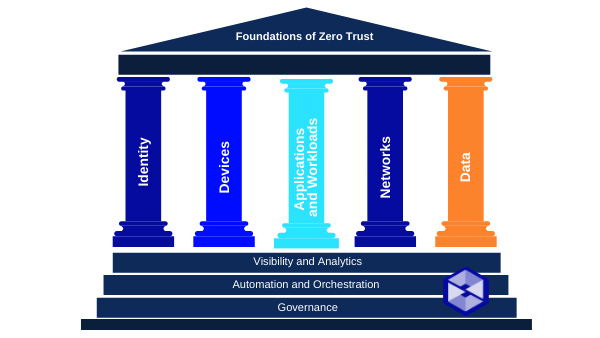
These goals are organized using the Zero Trust (ZT) maturity model developed by the Cybersecurity and Information Security Agency (CISA). The Zero Trust model describes five complementary areas of effort (pillars): Identity, Devices, Networks, Applications and Workloads, and Data, with three themes across these five areas; Visibility and Analytics, Automation and Orchestration, and Governance.
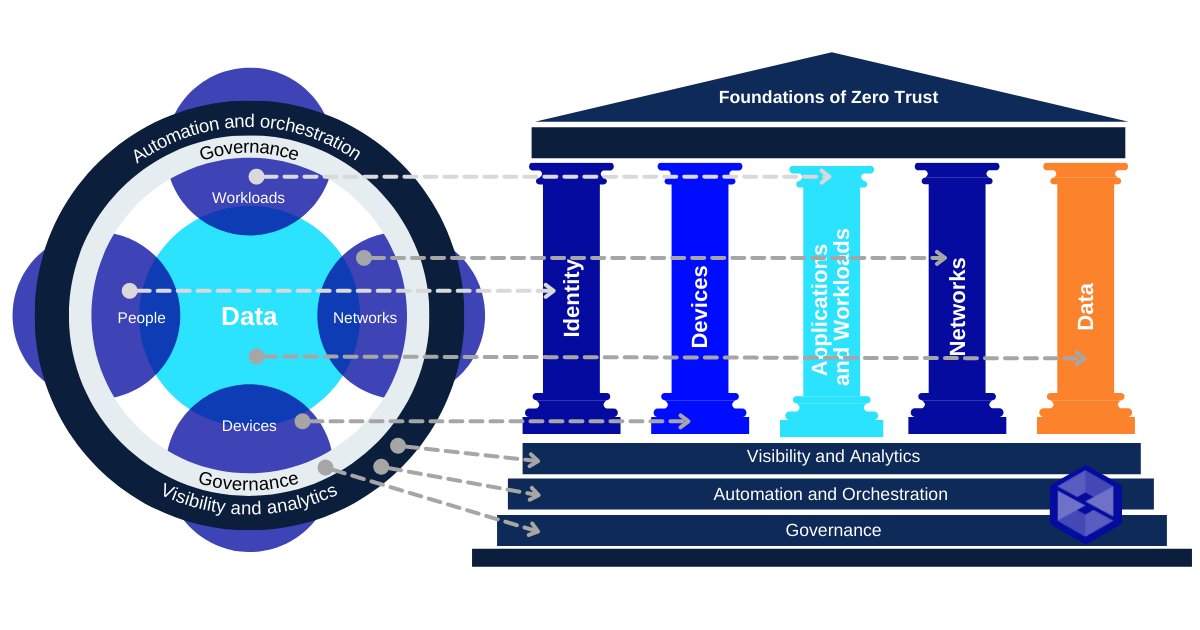
CISA’s five pillars can be described as:
1. Identity: Agency staff use enterprise-managed identities to access the applications they use in their work. Phishing-resistant Multi-Factor Authentication (MFA) protects that personnel from sophisticated online attacks.
2. Devices: The Federal Government has a complete inventory of every device it operates and authorizes for Government use, and can prevent, detect, and respond to incidents on those devices.
3. Networks: Agencies encrypt all DNS requests and HTTP traffic within their environment, and begin executing a plan to break down their perimeters into isolated environments.
4. Applications and Workloads: Agencies treat all applications as internet-connected, routinely subject their applications to rigorous empirical testing, and welcome external vulnerability reports.
5. Data: Agencies are on a clear, shared path to deploy protections that make use of thorough data categorization. Agencies are taking advantage of cloud security services to monitor access to their sensitive data, and have implemented enterprise-wide logging and information sharing.
Situational Awareness
M-22-09 directs agencies to highest-value starting points to ZT architecture. The Office of Management and Budget (OMB) and CISA will work with agencies throughout their Zero Trust implementations to capture best practices, lessons learned, and additional agency guidance and make that available on a jointly maintained website at zerotrust.cyber.gov.
Action Items
- DO make use of rich security features present in cloud infrastructure.
- DO achieve specific Zero Trust security goals by end of FY2024.
- By February 25th (30 days from release of M-22-09) designate and identify a Zero Trust strategy implementation lead for the agency.
- By March 27th (60 days from release of M-22-09) agencies that developed their plan for implementing ZT under EO 14028 must incorporate these additional requirements and submit an implementation plan for FY22-FY24 for OMB concurrence and budget estimate.
- DO internally source funding in FY22 and FY23 to achieve priority goals or seek funding from working capital funds or the Technology Modernization Fund (TMF).
This is the first in a series of blog posts on Zero Trust and M-22-09. Each week, Swish will publish a new post covering the Summary, Situational Awareness Items, and Agency Action items for each section of the Memorandum. Swish Engineering POCs are available for individual discussions as well and can be reached at: info@swishdata.com.





