Moving Beyond Compliance
Civilian Agencies have an opportunity to evolve their security capabilities beyond the compliance mandates in the M-22-09 Device Pillar for Asset Inventories and End Point Detection (EDR).
In this article, we’ll discuss what to ‘do’ and ‘not do’ to meet compliance mandates, as-well-as, streamline security operations and budgets.
Inventory Assets
Situational Awareness:
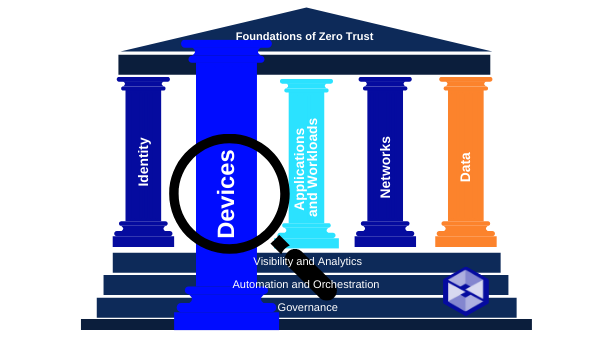
A necessary foundation of Zero Trust (ZT) is a complete understanding of devices, users, and systems interacting within an organization. For most organizations, this requires tools that support dynamic discovery and cataloging of assets.
CISA’s CDM program offers a suite of services in support of improved detection and monitoring of assets.
Action Items:
- DO ensure that your agency has formalized their CDM participation as directed in EO 14028 via a memorandum of agreement with DHS.
- DO create ongoing, reliable, and complete asset inventories, leveraging the CDM program. This is especially practical in cloud environments with rich, granular and dynamic permission systems.
Government-wide Endpoint Detection and Response
Situational Awarenss:
Agencies are required to support EO 14028, OMB issued Memorandum M-22-01, Improving Detection of Cybersecurity Vulnerabilities and Incidents on Federal Government Systems Through Endpoint Detection and Response.
Action Items:
- DO ensure your agency’s EDR tools meet CISA’s technical requirements and are deployed and operated across the enterprise.
- DO work with CISA to identify implementation gaps, coordinate deployment of EDR tools and establish information sharing capabilities as described in M-22-01.
- DO expect to establish procedures and technical processes to make information reported from EDR tools available to CISA.
- DO NOT worry about mainframes, thin clients, or IoT devices for EDR but employ defenses from other zero trust mechanisms to mitigate risk. Examples include micro segmented VLANs and extra behavioral analysis.
Opportunities for Improvement:
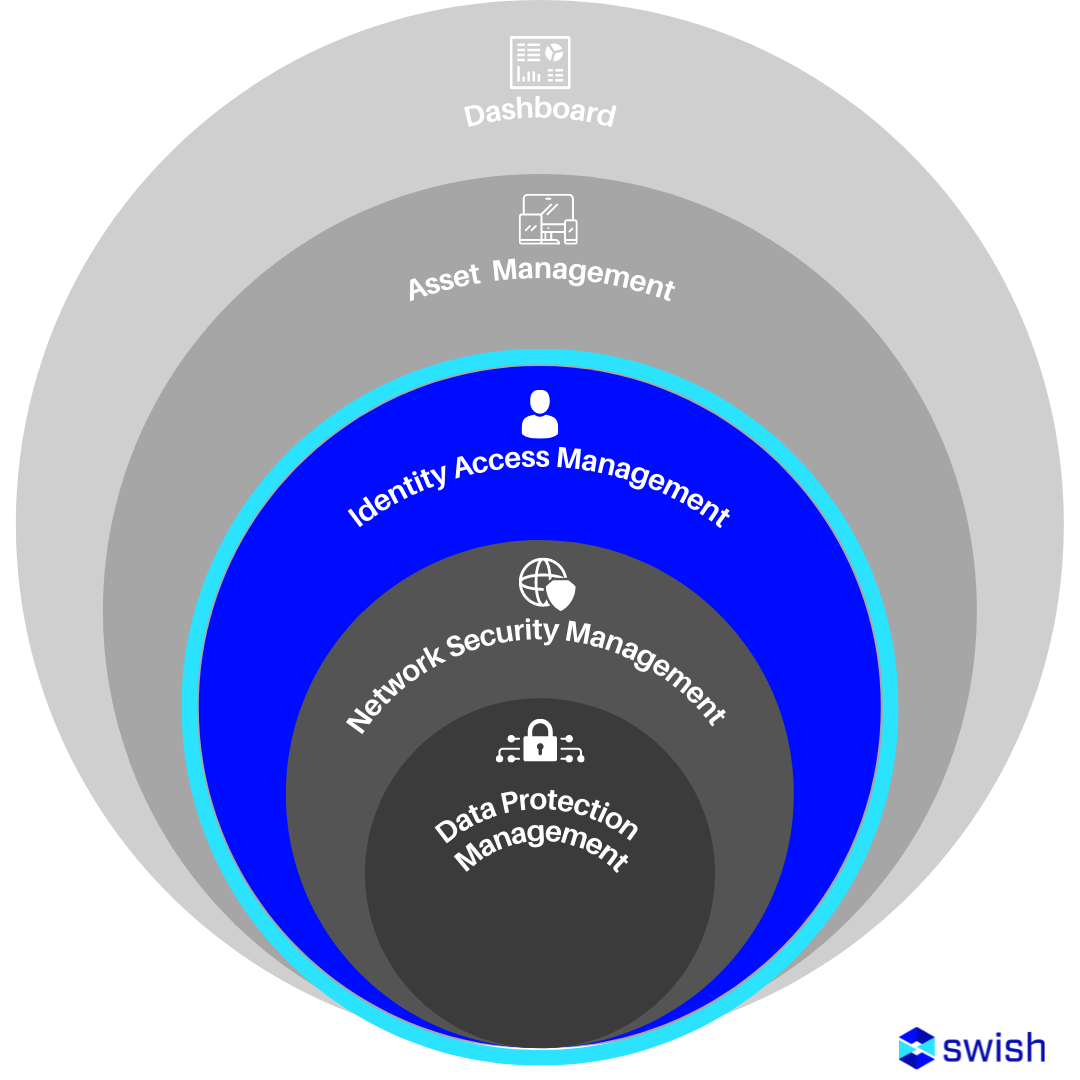
Agencies must approach inventory and detection and response in a holistic and modern manner. There are many types of devices, including servers, virtual machines, containers, IoT, SCADA, ICS and mission-specific assets. Furthermore, detection and response are no longer focused just at the endpoint, but more importantly, have evolved into Extended Detection and Response (XDR). Approaching Detection and Response from just the End Point perspective creates silos of data, creates friction for Hunt teams to investigate holistically, and ultimately costs more.
No Funds, No Worries
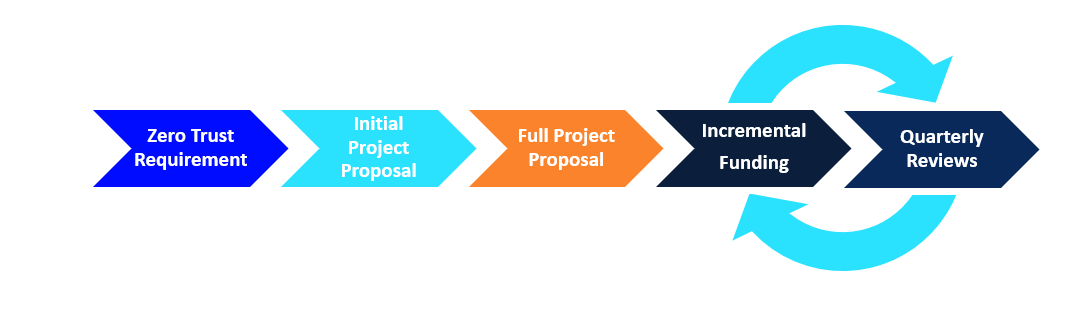
As mentioned in the M-22-09 Summary post, agencies should internally source funding in FY22 and FY23 to achieve priority goals or seek funding from working capital funds or the Technology Modernization Fund (TMF). Swish has experience working with Civilian and DoD entities assisting in their proposal process for working capital funds as well as TMF. For TMF especially, Swish has a detailed understanding of the two-phased approval process and can directly assist your agency with the Initial Project Proposal (IPP) and the Full Project Proposal (FPP).
Roll Up Your Sleeves with Swish
Swish focuses on delivering outcomes as our priority. Agencies can ‘check the box’ while also rationalizing their architecture, streamlining their operations, and gaining benefits from AI/ML technologies. Contact us to learn more!
To read more about Zero Trust you can find our summary post here, and our Identity post here.