

On September 11, 2023, MGM Resorts, one of the largest casino operators in the world, suffered a ransomware attack causing widespread disruption to the company’s operations, with outages reported at multiple properties in Las Vegas and other locations. While the exact details of how the hackers gained access to MGM Resorts’ systems are still unknown, it is believed that the attack began with a simple social engineering attack against an IT support vendor employed by Caesar’s Entertainment, a rival casino operator, and from this we can glean a few key things from the available information:
- First, the hackers were able to gain access to MGM Resorts’ systems with elevated privileges. This allowed them to deploy ransomware and disrupt the company’s operations.
- Second, it’s likely that the hackers used a zero-day exploit to gain access to mission critical systems. A zero-day exploit is a vulnerability in software that is unknown to the software vendor. This makes it difficult to detect and prevent attacks that exploit zero-day vulnerabilities.
- Third, the ransomware used in the attack was likely a very sophisticated variant that was able to evade MGM Resorts’ security measures.
In a social engineering attack, hackers attempt to trick people into revealing confidential information or performing actions that compromise security. In this case, the hackers were able to impersonate an MGM Resorts employee and convince the IT support vendor to grant them access to the company’s systems. Once the hackers had access, they were quickly able to deploy ransomware, a type of malware that encrypts data. Once this is done, the hackers will demand a ransom payment, often in cryptocurrency, to decrypt them.
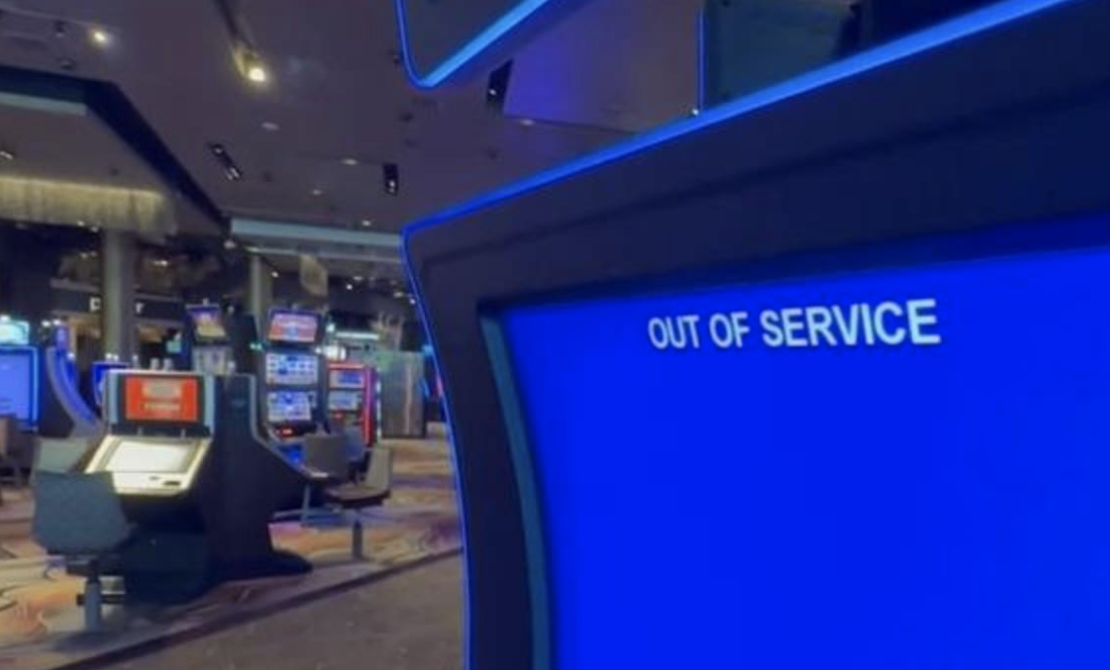
The attack caused widespread disruption to MGM Resorts’ operations taking down slot machines, table games, hotel booking systems, and other critical systems. The real financial impact on MGM Resorts is likely still being calculated, but the company reported a $100 million loss in revenue in the third quarter of 2023 due to the attack. Having a good cybersecurity posture is key in today’s day and age, but most enterprises are overlooking a key piece of the strategy: Backups.
Consider this timeline of events:
- September 7: A social engineering attack is launched against the IT support vendor employed by Caesar’s Entertainment by hacking gang Scattered Spider.
- September 11: MGM Resorts suffers a cybersecurity attack, with system outages reported at multiple properties, including the Bellagio, Mandalay Bay, Mirage, and Park MGM.
- September 12: MGM Resorts confirms the attack and states that it is investigating the incident. The company also announces that it has taken several steps to mitigate the impact of the attack, including isolating affected systems and deploying additional security measures.
- September 13: MGM Resorts releases a statement saying that the attack was caused by ransomware and that the company is not paying a ransom. The company also states that it has no evidence that any customer data was compromised.
- September 14: MGM Resorts begins to restore affected systems and services.
- September 15: MGM Resorts announces that all affected systems and services have been restored.
- September 16: MGM Resorts releases a statement saying that it is continuing to investigate the attack and that it is working with law enforcement to identify the perpetrators.
- September 27: MGM Resorts has not yet released any further information about the attack or the investigation.
A good backup and recovery plan can significantly reduce the impact of a ransomware attack and could have saved MGM millions of dollars in lost revenue and manpower. If the company had employed regular backups of its critical systems, it could have simply restored them from those backups soon after the attack and minimized the disruption to its operations. However, it is important to note that not all backups are created equal. To be effective against ransomware attacks, backups must be:
- Regular: Backups should be performed on a regular basis, such as daily or weekly, to ensure that you have a recent copy of your data in case of a ransomware attack. The frequency of your backups will depend on your specific needs and how often your data changes. If your data changes frequently, you may want to consider performing backups more often.
- Comprehensive: Backups should include all critical systems and data, including operating systems, applications, databases, and user files. This will ensure that you can restore your data completely in the event of a ransomware attack.
- Properly Stored: Store your backups on a cloud storage service, such as Amazon S3 or Microsoft Azure Blob Storage. Alternatively, you can store your backups on a physical device, such as an external hard drive or tape drive, and keep it in a safe location, such as a bank vault. Immutable storage is another way to protect your backups, allowing you to store your backups in a way that makes them invulnerable to ransomware encryption, such as using a write-once, read-many (WORM) device or a blockchain-based backup service.
The MGM Resorts hack is a reminder of the growing threat of ransomware attacks against businesses of all sizes. Social engineering attacks are a major threat and Businesses need to train their employees on how to identify and avoid social engineering attacks as well as use strong measures to ensure they’re secure, such as multi-factor authentication, strong passwords, regular security updates, and of course robust backups.

