Introduction
Software Bill of Materials (SBOM) requirements are becoming increasingly important for government agencies as they seek to ensure the security and integrity of their software systems. By creating and maintaining an SBOM for all software, organizations can better understand the makeup of their software and identify any potential vulnerabilities that may exist. For further discussion on the basics of SBOM check out my previous blog Software Bill of Materials Simplified.

Unlocking the Value of SBOM
Unlocking the full value SBOM across an enterprise requires a coordinated effort and adoption of several components and automated tools. Here are a few steps to unlock the value of SBOM for your enterprise.
● You need almost complete adoption of SBOM as a requirement across the enterprise (See Cyber Security EO & OMB Memo). Without widespread implementation, the processes and procedures required to create and use SBOM create extra work without adding value.
● Next you need an organizational database containing all information relative to SBOM. This presents security concerns as this information and central database would be highly sensitive to compromise as a road map to enterprise vulnerabilities.
● Then the implementation must be centrally managed in order to be efficient and requires careful security controls to prevent exploitation. For vulnerability reporting and remediation, vulnerability management and integration into Security Orchestration, Automation, and Response (SOAR), tools are vital to unlocking the full potential. For the DOD the Information Assurance and Vulnerability Management (IAVM) process must be integrated with Vulnerability Exploitability eXchange (VEX) to maximize the value of SBOM.
● Next you need real-time visibility of vulnerabilities tracking through SBOMs and related to enterprise SIEM for correlation.
● Then you need a means to automate patch implementation for all affected software when a patch becomes available. The biggest challenge for implementing automated distributed patching using SBOMs is managing the risk of unforeseen software outages. Outages caused by automated patching could increase the risk of software failure in critical systems if automated patching is implemented improperly. Thus critical systems would require more oversight before allowing patches to be pushed.

A Deeper Dive
Now it is time to take a look at implementation.
Generating SBOM is simple in concept but much more difficult to implement in a way that unlocks its full value.
It is fairly simple to generate SBOM reports for software. But enforcing a standardized process for all software adopted for an enterprise, and storing and using this information efficiently is far more difficult.
Manually managing SBOMs for an enterprise is a process-intensive task with open source and even COTS offerings, including increasingly interdependent code sources. The proper way to manage SBOM for the enterprise is to use a SBOM Repository tool such as the one by Anchore. This enables automated responses and enterprise-wide patching by tracking the dependency tree of affected code.
For even better integration, this would be used alongside VEX to verify that the vulnerabilities tracked are present in each implementation. This uses a machine-readable artifact that is attached to a SBOM and allows software manufacturers to communicate the status of vulnerabilities discovered in software components and validate them for a specific piece of software.
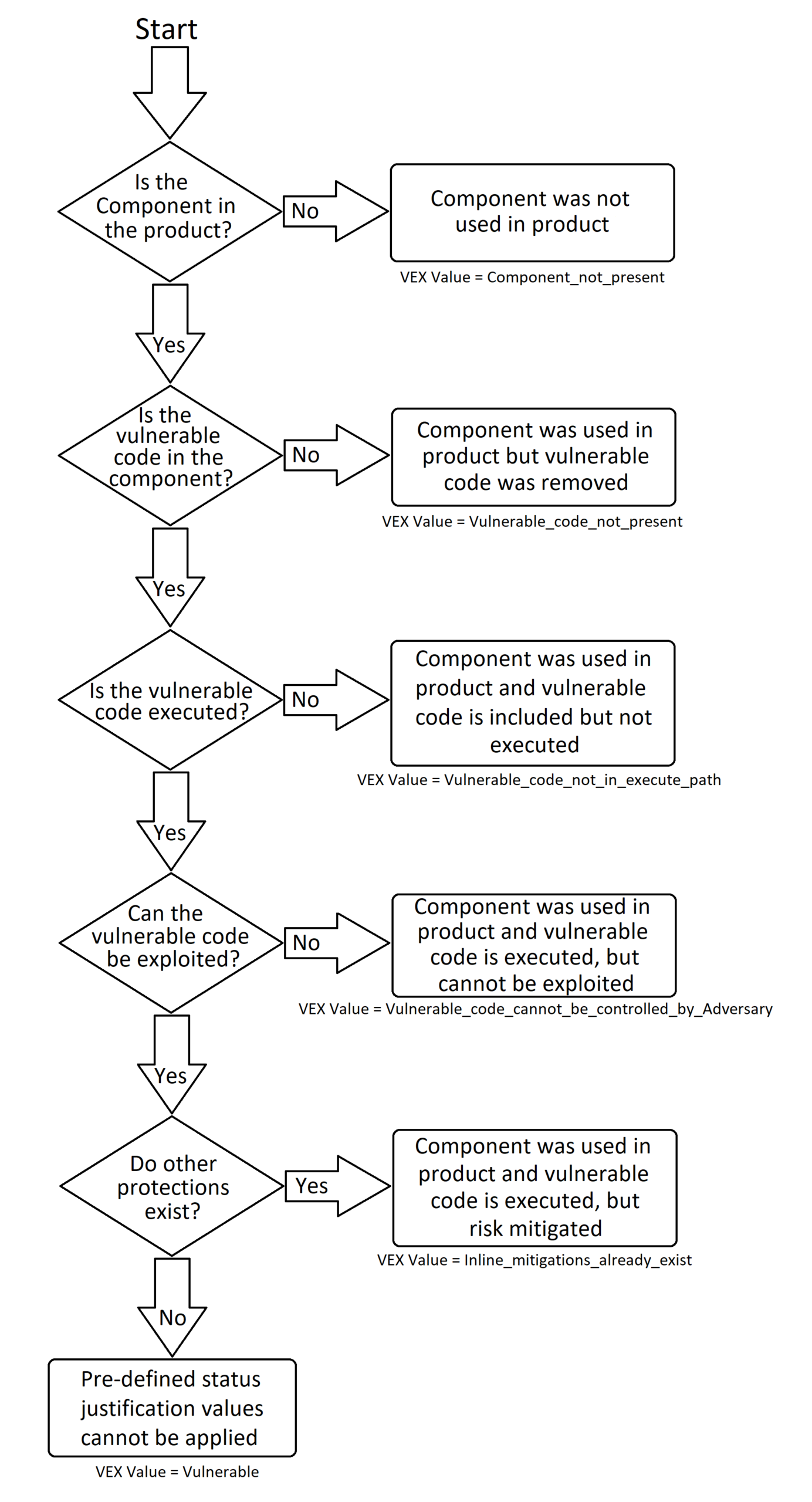
The following chart shows the way VEX can be used to track and update SBOMs with relevant vulnerability information and eliminate false positives for unaffected or patched software.
VEX Exploit Relevance Flow Chart
Advantages of using VEX:
● Eliminate a majority of false positives
● Address instances where a vulnerability cannot be exploited, due to implementation or other controls
● Convey the manufacturer’s progress on a mitigation for the vulnerability
● Recommend workarounds
● Availability of a patch or mitigated new version
– Reference: NTIA SBOM Framing and Sharing
VEX enables security managers to have an accurate, real-time view of vulnerabilities that effect their organization without the long lead time and manual investigation. It can then be further used to automate remediation based on the informed software triage.
The fundamental purpose of SBOM implementation is to provide a framework for software dependencies that lends itself to automation for vulnerability management and enables DevSecOps teams to maintain visibility of the status of their code throughout the Continuous Integration and Continuous Delivery process (CI/CD pipeline).
Taking the Next Step
As Federal mandate deadlines draw near and SBOM integration in the DevSecOps space matures, let Swish help you with your transition and improve your security posture and vulnerability management efficiency. Swish is partnered with industry leaders Anchore, Gitlab and Checkmarx in providing industry leading tools for SBOM management and CI/CD pipeline integration for Federal agencies and the Department of Defense.
Federal Mandates
Executive Order on Improving the Nation’s Cybersecurity (See Section 4)
OMB Memo (See Section 1: Self-Attestation Requirement)





