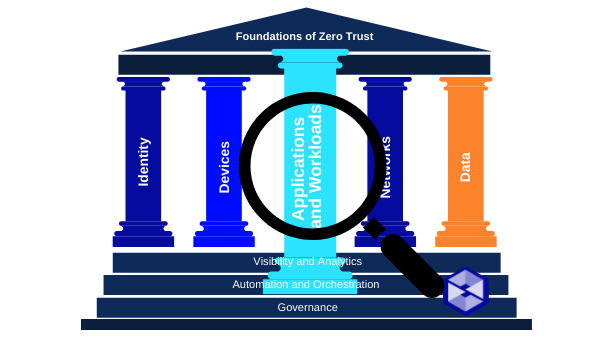
Applications and Workloads
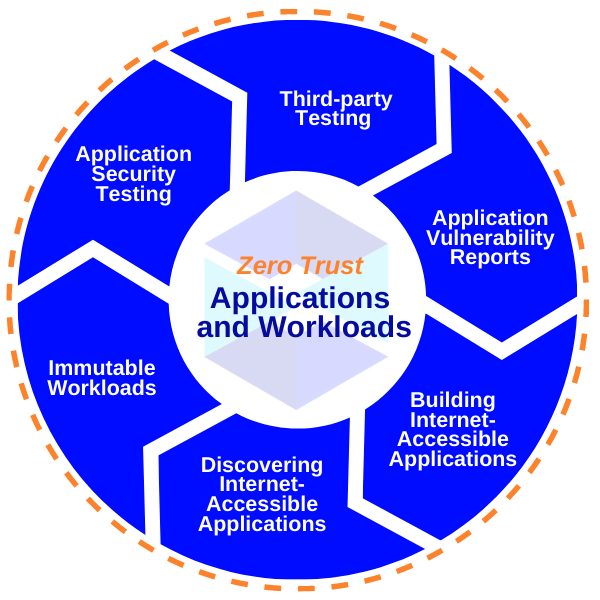
In our fourth breakdown of the Applications and Workloads Pillar requirements as outlined in M-22-09, we will discuss the pillar summary, necessary situational awareness items, and action items for agencies responsible for meeting the mandate. This section is broken into six topics: application security testing, third-party testing, application vulnerability reports, building internet-accessible applications, discovering internet-accessible applications, and immutable workloads.
Applications and Workloads – Bottom Line Up Front (BLUF)
- Agencies must operate dedicated application security testing programs.
- Agencies must utilize high-quality firms specializing in application security for independent third-party evaluation.
- – CISA and GSA will work together to make these services available for rapid procurement.
- Agencies must maintain an effective and welcoming public vulnerability disclosure program for their internet-accessible systems.
- Agencies must identify at least one internal-facing FISMA Moderate application and make it fully operational and accessible over the public internet.
- CISA and GSA will work together to provide agencies with data about their online applications and other assets.
- – Agencies must provide any non-.gov hostnames they use to CISA and GSA.
- Agencies should work toward employing immutable workloads when deploying services, especially in cloud-based infrastructure.
Application Security Testing
Situational Awareness
Agencies should already have a Security Assessment Report (SAR) as part of authorizing their information systems. These SARs should incorporate not just information gathered by automated tools for vulnerability scanning and code analysis of custom-developed software, but also analysis prepared by more time-intensive, specialized, and application-specific methods.
Action Items
DO employ a system authorization process that utilizes automated analysis tools and manual expert analysis.
DO, as directed in EO 14028, follow the NIST developed guidelines for developer verification of software which should inform agencies of strategies, methodologies, and standard processes for application testing.
Easily available third-party testing
Situational Awarness
Agencies must increase reliance on external perspectives to identify vulnerabilities that internal staff may not identify.
Action Item
DO collaborate with CISA and GSA within 1 year of this release (26, Jan 2023) to create a procurement structure to allow for rapid acquisition of rigorous application-security testing capabilities.
Welcoming Application Vulnerability Reports
Situationl Awareness
To ensure agencies are able to receive vulnerability information from the general public, OMB issued Memorandum M-20-32, and CISA published Binding Operational Directive 20-01. Those authorities require agencies to publish security contact information as a welcoming vulnerability disclosure policy (VDP).
CISA has released a vulnerability disclosure platform that agencies can use to receive and triage vulnerability reports and to engage directly with security researchers.
Action Item
DO use the CISA vulnerability disclosure platform to receive and triage vulnerability reports and to engage directly with security researchers.
Safely Making Applications internet-accessible
Situational Awareness
The goal is to make applications safely accessible without a VPN or network tunnel through the internet.
Action Items
DO select one FISMA moderate system that requires authentication and is not currently internet accessible. Within 1 year of the release (26, Jan 2023), allow secure, full-featured operation of that system over the internet.
DO put in place minimum viable monitoring infrastructure, Denial-of-Service protection, and enforced access control policy for this FISMA moderate system.
DO NOT accomplish via VPN or network tunnel.
Discovering internet-accessible applications
Situational Awareness
To effectively implement a Zero Trust architecture, an organization must have a complete understanding of its internet-accessible assets, so that it can apply security policies consistently and fully define and accommodate user workflows. To build a complete understanding of internet-accessible attack surfaces, agencies must rely not only on internal records but also on external scans of infrastructure from the internet.
Action Items
DO leverage CISA provided data about agencies’ internet-accessible assets.
DO, within 60 days of the issuance of this memo (26, Jan 2023), assist CISA and GSA’s efforts to track the use of Federal non-.gov web URLs by providing non-.gov hostnames used by internet-accessible information systems.
Immutable Workloads
Situational Awareness
Mature cloud-based infrastructure typically offers technical interfaces that are well optimized for fully automated deployment strategies and can support deployment and roll-back practices that confer fundamentally improved security properties (also known as DevSecOps).
Action Items
DO deploy code or infrastructure to a cloud environment in a way that technically restricts manual modification to enable a homogenous environment.
DO use CISA’s Cloud Security Technical Reference Architecture (TRA) as a guide for migrating third-party services from on-premise hosting to cloud infrastructure providers.
Opportunities for Improvement
This section focuses on treating all applications as internet-connected, routinely subjecting applications to rigorous empirical testing, and welcoming external vulnerability reports. Ultimately, principles of least privilege are enforced throughout the application lifecycle and risks are minimized while improving connectivity and productivity of users.
This is the fourth in a series of blog posts on Zero Trust and M-22-09. You can find the first post here along with posts on Identity and Devices. Each week, Swish will publish a new post covering the Summary, Situational Awareness Items, and Agency Action items for each section of the Memorandum. Swish Engineering POCs are available for individual discussions. Contact Us to learn more!

